Series Blog 4: Operationalizing Regulatory Architecture
Understanding regulatory principles is only the first step. The more difficult challenge lies in operationalizing those principles within live systems.
Moving from compliance design to production deployment requires coordination between architecture, legal, operations, and security teams.
Embedding Compliance into Operational Workflows
Rather than treating compliance as a reporting function, mature architectures embed regulatory controls into transaction workflows.
Examples include:
• Multi-level approval processes before transaction finalization
• Automated logging of authorization events
• Clearly defined retention and archival policies
• Defined escalation paths for exceptional cases
These controls are implemented primarily in enterprise application logic and governance frameworks. Blockchain serves as a verifiable execution and recording layer.
SIX Garage and related tooling can assist in structuring asset management and permission workflows, but they operate within broader governance systems defined by the organization.
Monitoring and Continuous Oversight
Production systems require observability. Compliance does not end at deployment; it requires continuous oversight.
Architectural monitoring typically covers:
• Transaction latency and failure rates
• Role misuse or unauthorized access attempts
• Data consistency across on-chain and off-chain components
• Audit trail completeness
SIX Network infrastructure can be integrated into existing monitoring frameworks, allowing blockchain operations to be managed alongside other enterprise systems.
From Policy to Implementation
Regulatory frameworks such as GDPR, HIPAA, SOX, or AML/KYC define principles. Implementation varies by jurisdiction and organization.
No protocol can automatically guarantee compliance across all contexts. Instead, infrastructure should provide flexibility and traceability that enable organizations to implement their own compliance interpretations.
SIX Network’s approach emphasizes architectural support rather than automated regulatory guarantees.
Conclusion
Enterprise blockchain deployment in regulated environments requires architectural rigor, governance clarity, and operational discipline.
SIX Network’s standards-based protocol and supporting tools are designed to align with these enterprise requirements, not to replace them.
By approaching integration and compliance as architectural challenges rather than marketing features, organizations can move toward sustainable, production-ready blockchain adoption.
⎯⎯⎯⎯⎯⎯⎯⎯⎯⎯⎯⎯⎯⎯⎯⎯⎯⎯⎯⎯⎯⎯⎯⎯⎯⎯⎯⎯⎯⎯⎯⎯
Disclaimer:
1.This article is intended for informational purposes only. Please conduct your own research before making any investment decisions related to cryptocurrencies 2. Cryptocurrency and digital token involve high risk; investors may lose all investment money and should study information carefully and make investments according to their own risk profile.

Warisara Thepsiri
Experience the magic of Blockchain with SIX Network!
Related Posts

SIX Network ประกาศความร่วมมือกับ Selanet ผู้โครงสร้างพื้นฐานสำหรับ AI Agents
SIX Network ประกาศความร่วมมือกับ Selanet ผู้พัฒนา Infrastructure สำหรับ AI Agents เพื่อขับเคลื่อน Web3 Ecosystem เรามีความยินดีอย่างยิ่งที่ได้ประกาศความร่วมมือกับ Selanet ผู้พัฒนาโครงสร้างพื้นฐานดิจิทัลที่ช่วยให้ AI agents สามารถทำงานบนเว็บไซต์ต่าง ๆ

SIX Network Announces Partnership with Selanet AI Infrastructure
SIX Network Partners with Selanet, AI Agent Infrastructure Developer, to Drive Web3 Ecosystem Growth We are pleased to announce

SIX Network Roadmap 2026: Institutional Assets and Financial Infrastructure
Recap 2025: From Infrastructure to Real World Execution In 2025, SIX Network moved beyond building blockchain infrastructure and began
Series Blog 4: Operationalizing Regulatory Architecture
Understanding regulatory principles is only the first step. The more difficult challenge lies in operationalizing those principles within live systems.

Series Blog 3: Designing Blockchain for Regulatory Alignment
Enter to Blog 3: How Blockchain Architecture Can Be Built for Compliance and Regulatory Compliance concerns often surface early
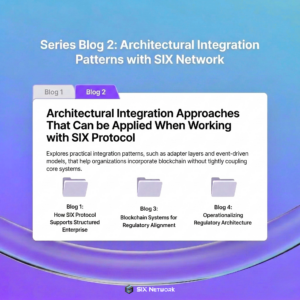
Series Blog 2: Architectural Integration Patterns with SIX Network
Enter to Blog 2: Architectural Integration Patterns with SIX Network In the previous article, we discussed how standards alignment,